Token impersonation | Active Directory | Windows Privilege Escalation | Cyber Security for Beginners - YouTube

Implement the OAUTH 2.0 Token Exchange delegated flow between an Azure AD API and an API protected using OpenIddict | Software Engineering
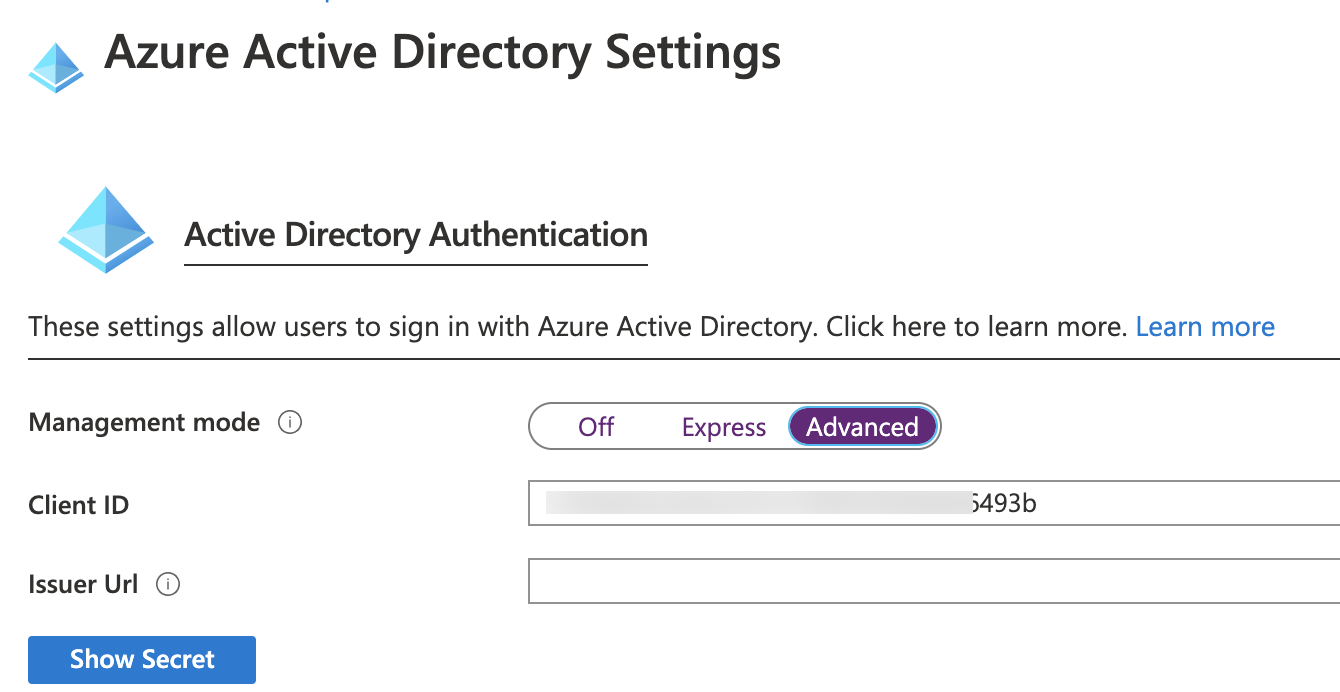
Impersonation within Azure Function or Custom Connector when using AAD authentication - Microsoft Dynamics 365 CRM Tips and Tricks
.png)